As an IT Professional, you know the value of having a strong security posture; you’ve got your firewalls in place, endpoint protection on all your employee laptops, and appropriate access measures in place to ensure that only the right people have access to secured documents and data…but did you know that a large portion of data breaches are a result of the employees that you trust to run your business?
While your employee may not maliciously be clicking on phishing emails, they cause the same financial and reputation damage as direct hacking attempts. How can you help to arm employees with knowledge about security threats and simple ways to avoid falling prey to bad actors?
Ingram Micro offers two unique approaches to helping both understand the vulnerability of your workforce as well as to educate on today’s threats and attack vectors: CyberSAFE Training, and Social Engineering Assessments. The spring is a great time to focus on getting employees up to speed – think of it as Security Spring Training!
CyberSAFE Training
According to Reuters, end-user awareness and training reduces security-related risks by 45% to 70%, and when partnered with a Social Engineering Assessment, businesses can truly measure employee adherence to the training topics.
CyberSAFE Training is an online learning module designed for non-technical end users of computers, mobile devices, networks, and the Internet. The CyberSAFE training allows organizations to increase their security posture quickly and with minimal investment by ensuring that end users are equipped with the knowledge necessary to be good stewards of organizational data and access.
Social Engineering Assessment
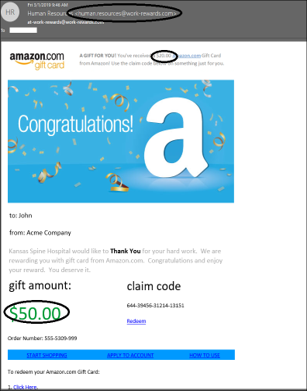
We’ve all received phishing messages that are clearly an attempt to gain information – but do your employees have these same instincts? Ingram Micro’s Social Engineering Assessment tests your employee base with spoofed emails and phone calls to determine who opens the message, who takes action with the message, and who enters information into the spoof form – which is the way that many hackers phish and spear-phish to obtain credentials, leading to the data breaches that we see on the news each week.
At the close of the assessment period, an executive presentation is made detailing the number of spoofs made, as well as the number of successful attempts alongside the names of who took action in order to remediate these behaviors in the future.
Using the CyberSAFE Training and Social Engineering Assessment in a company-wide security spring training exercise will help to not only educate employees, but also test their adherence and attention to the important principles presented in the training.
Get Off the Bench Today!
Interested in learning more?
Contact the Professional & Training Services team at proservices@ingrammicro.com or 1-800-456-8000 x76094!